Today I want to talk about a cool new feature that Microsoft recently released as public preview, Windows 365 Boot. With Windows 365 Boot, you can convert every Windows 11 Client into a Thin Client like experience, that let you access your Windows 365 CloudPC super easy.
Prerequisites
- At first, obviously you need at least one Windows 365 Machine that you want to connect to.
- At the time of writing this article, you need to have your Windows 365 Boot Client to be enrolled into Windows Insider Beta Channel:
Windows 365 Boot physical device requirements | Microsoft Learn - The Guided Scenario in Intune that I will use today, also requires the Windows 365 Boot Client to be enrolled into Windows Autopilot
- For an seamless experience it is recommended to enable SSO in the Windows 365 Provisioning Policy
Configuring the Guided scenario in Intune
To get started in Intune, we go to the Troubleshooting + Support Blade in Intune and select “Guided scenarios (preview)”.
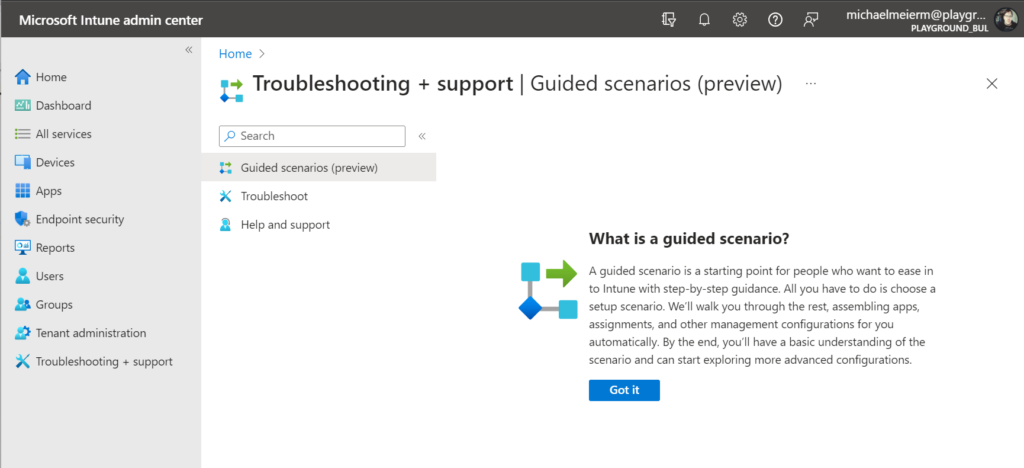
Once we confirmed the welcome message, we can select our scenario “Windows 365 Boot”.

The scenario starts with a nice overview, showing what it will do and how it is intended to be used.

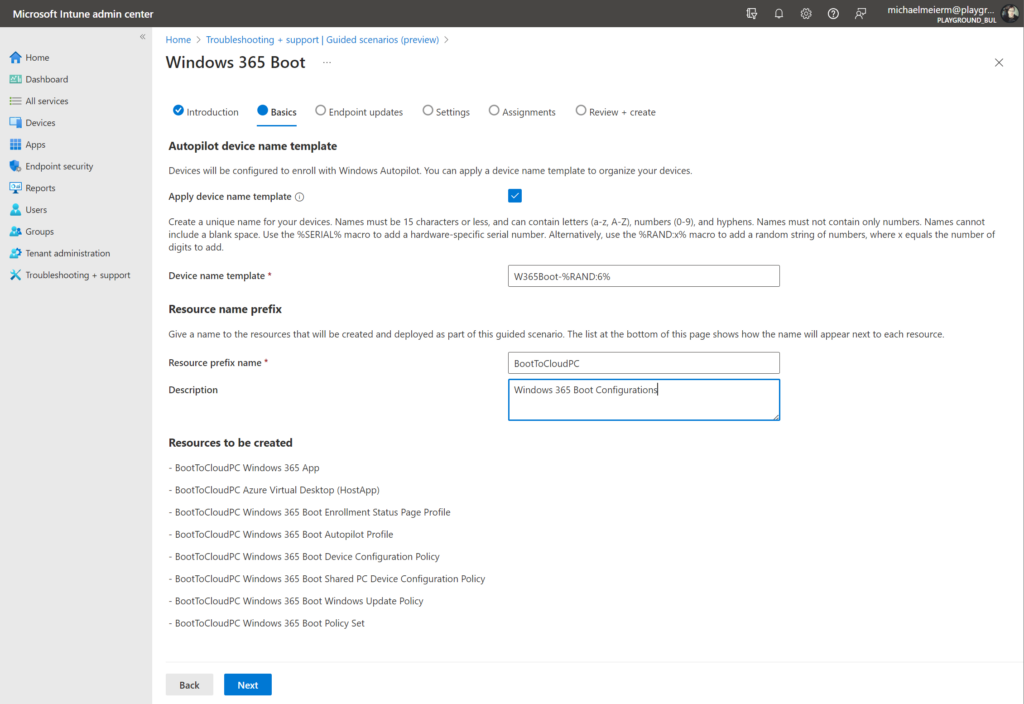
At the next page, you will be asked, if you want to apply a naming template for the newly created Autopilot Profile, and how the newly created Configuration Profiles and Apps should be named.
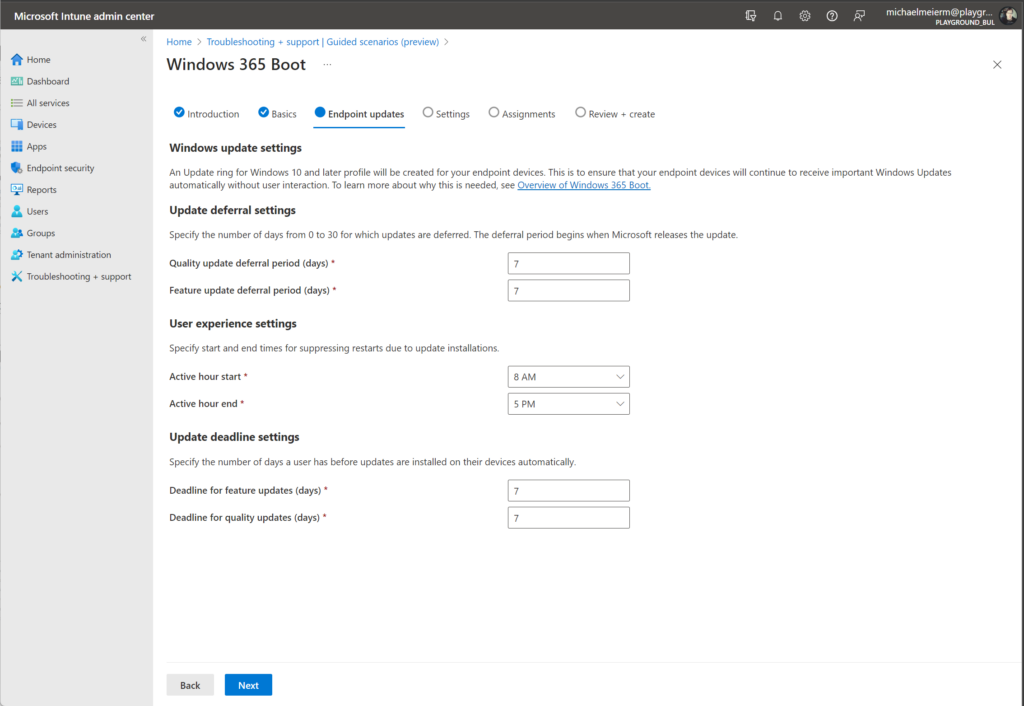
In the next page, you will be asked to configure the Windows Update related settings for the Windows 365 Boot Clients. For this demo I went with the default values. (You can always change these settings afterwards in the newly created Windows Update Ring for these devices)
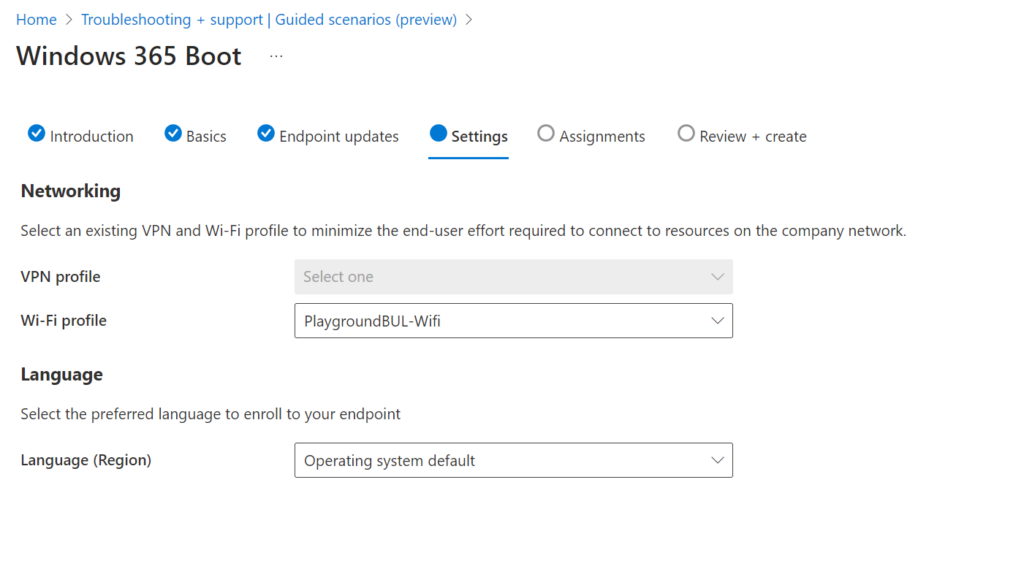
In the settings page, you can add an additional VPN or Wi-Fi profile if needed and select the language in which the device should be enrolled
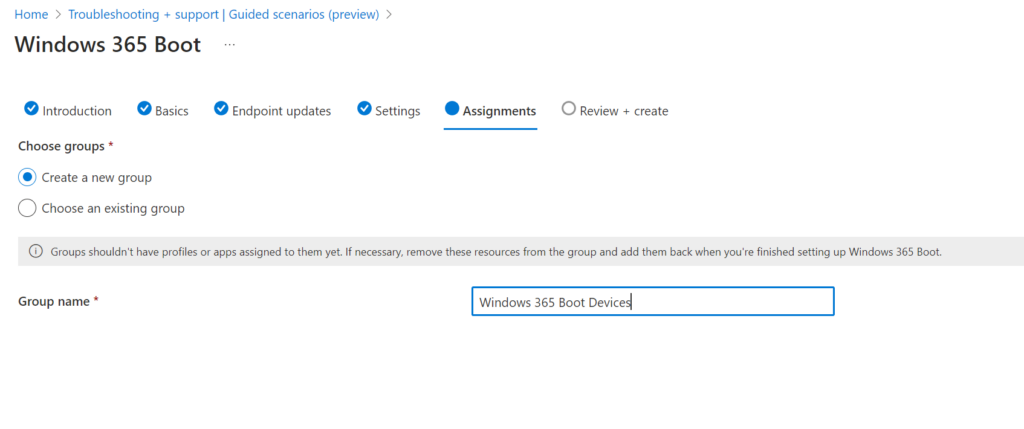
In the Assignments page, you can select a group of devices, that should be configured to use Windows 365 Boot. For this demo, I decided to create a new Group in this section, but you can also use an existing Device Group, or even a dynamic Device Group that filters for a specific GroupTag, if you so desire.
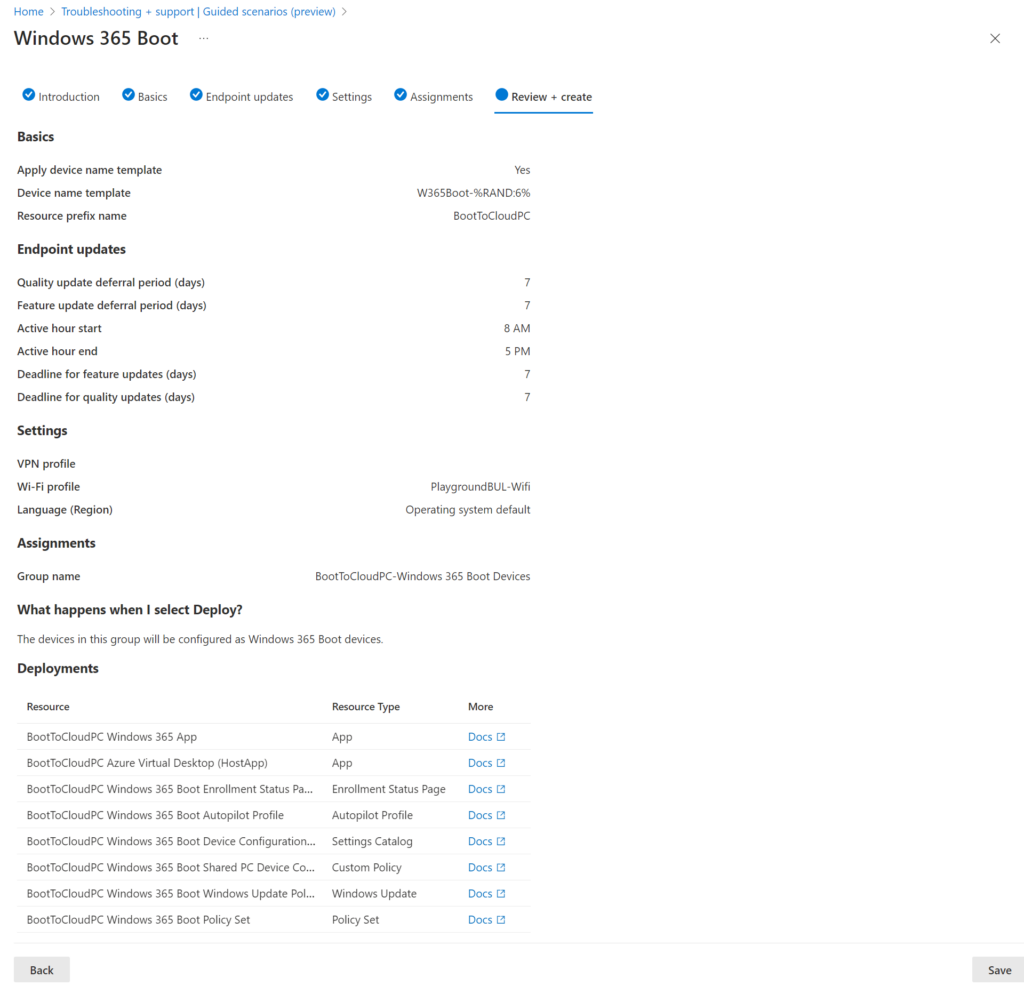
On the last page of this scenario, you will get a nice overview of the selected settings and a list of policies and apps that will be created once you click on save.
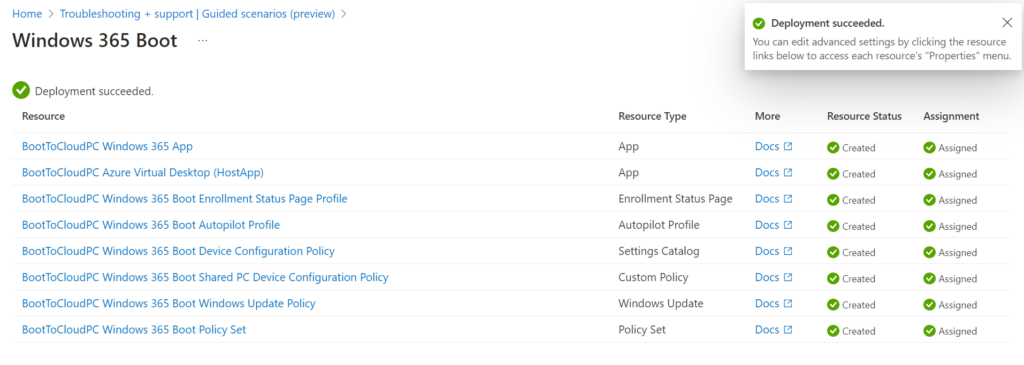
If everything went well, you will then see a deployment overview showing all of your settings and apps were created successfully and you can directly modify them if you need:
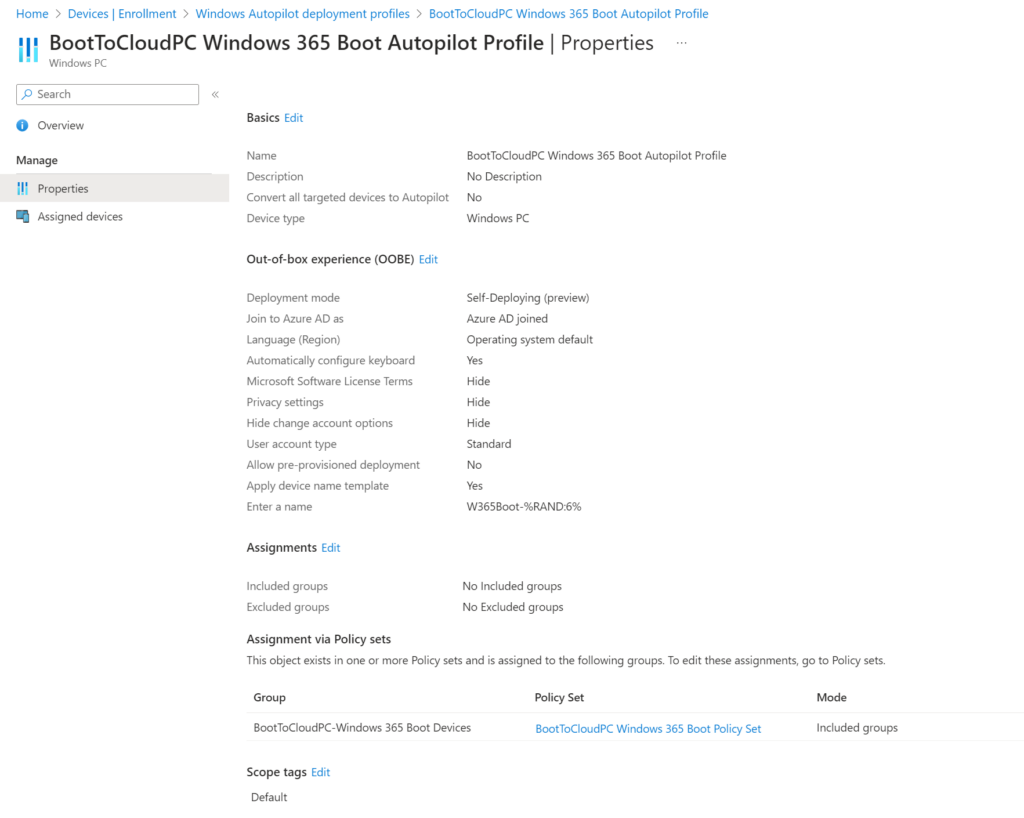
For this demo, I will modify the newly created Autopilot Profile to do a Self-deploying enrollment instead of a user-driven one to make the enrollment even simpler. Since you can’t change the Deployment mode of an existing Autopilot Profile, I decided to delete the existing once and create a new one. Just don’t forget to add the new Profile to the Policy Set, so the assignment is still working.

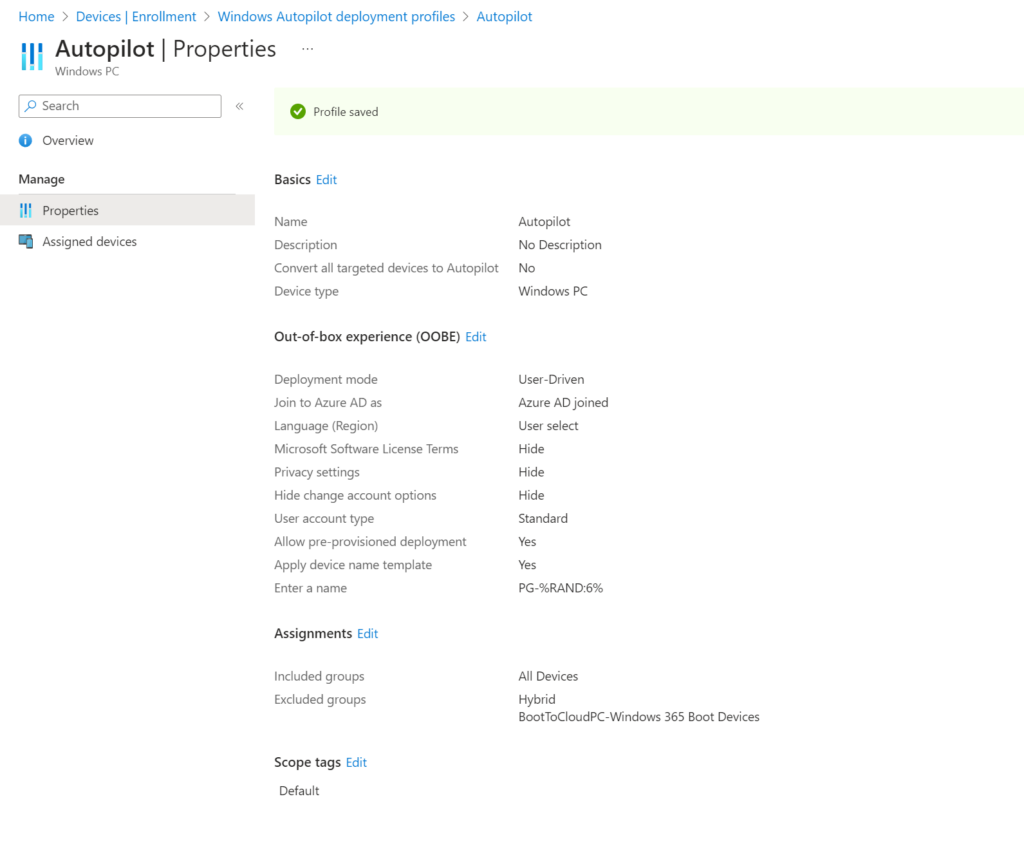
One additional Setting that I had to made in my environment, since my default Autopilot Enrollment Profile is assigned to “All Devices”, I had to exclude the Windows 365 Boot Devices from this Profile:
Once this was done, we are finished with the configuration of the scenario in Intune and we can start enrolling our first Windows 365 Boot Device.
Enrollment
The Enrollment of our new Windows 365 Boot Device will look like every Self-Deploying Autopilot device:
User experience
The experience for the user will look pretty similar to a logon to a “normal” device, once the logon is done via Username + Password or Fido2 Security Key, the user will be seamless redirected to the Windows 365 Machine
Conclusion
For me Windows 365 Boot is a really cool collection of settings like assigned access to replicate the look and feel of a Thin Client on a standard Windows device without the need of any additional tools. In my opinion this could be an ideal solution for either shared devices in production environments, where the frontline workers want to have “their own” PC regardless which terminal they are using.
In the future this could also be a nice solution for low-end devices, like power efficient laptops that are only used to display the much more powerful Windows 365 Machine

Leave a Reply