Today I want to talk about a really cool feature, which came with Intune Release 2306, driver and firmware management in Intune. While the backend service using Windows Update for Business Deployment Services (WUfB-DS) was available earlier, you had to create the policy’s manually via Graph API. Now with the seamless integration in Intune, it’s so much easier to manage these updates.
Prerequisites
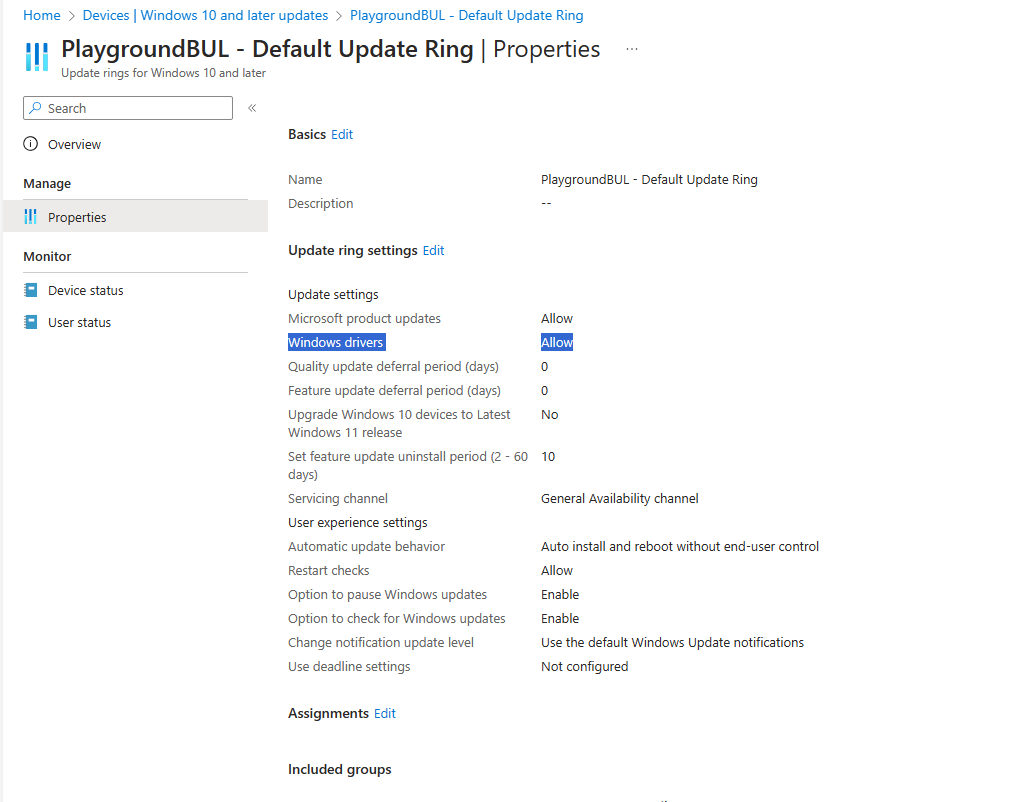
To start with driver and firmware management, we need a few things prepared, at first, we need to make sure, we have driver updates enabled in our WUfB Ring to make sure, the devices get driver and firmware updates offered.
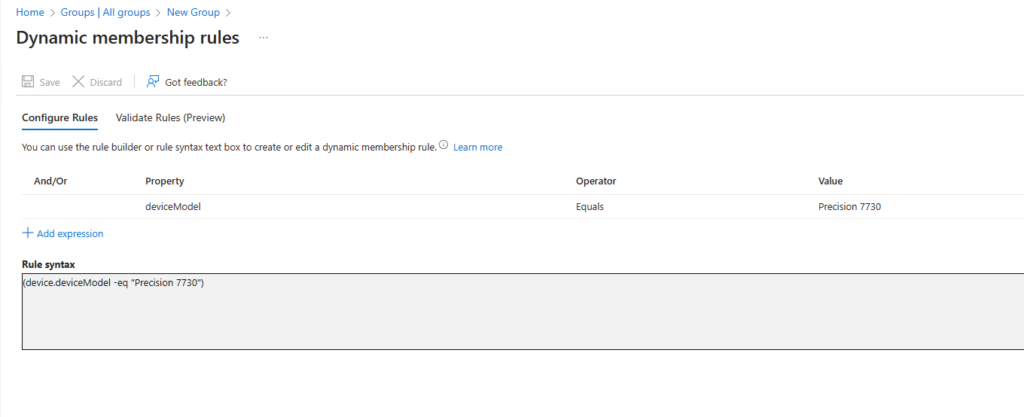
Next we need a Entra ID Group (AzureAD Group) that we use to target our new driver and firmware update policy. We are using dynamic groups that targets specific device models, as we want to manage driver and firmware updates on a per device model.

Automatic Update Policies
Now that we have our prerequisites fulfilled, we can start with our driver and firmware update policies. I will start with “Automatic” Policies, as we already had driver updates enabled in our WUfB Update Rings before, so there is not much change in the first glance.

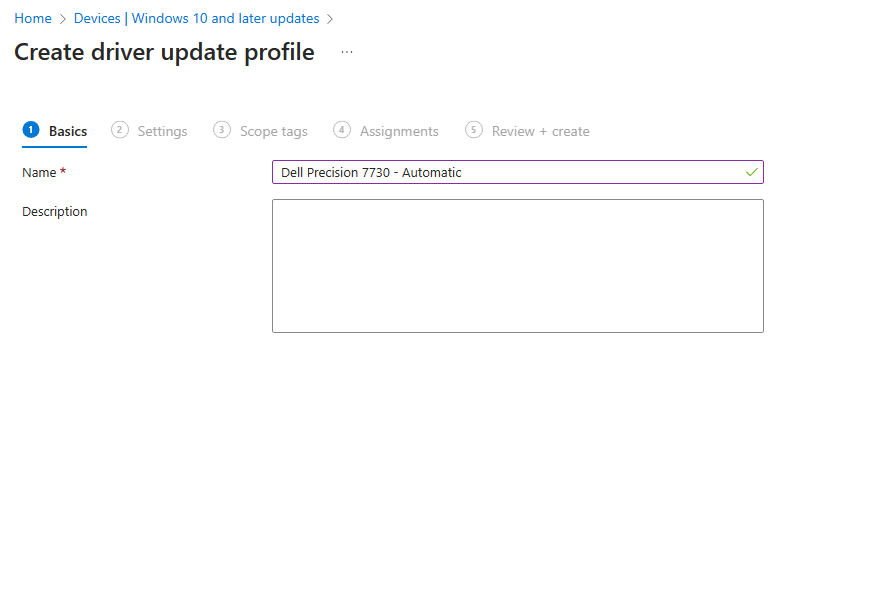
I decided to go with 0 days delay, as I do not have a Pilot Group for these devices, where I want to verify the results before.


Once we have created the policy and the first devices made a check-in to the WUfB-DS, we will see updates available in the portal. Since we created an automatic policy all “Recommended” update are automatically approved:

The nice thing of “Automatic” Policies for me is, that it allows me to have all recommended drivers automatically approved and give me the possibility to still specifically block a non-working update if needed. Also one of the coolest features in my mind, is the fact that we now can approved an “Other” driver that without WUfB-DS was not installed automatically for our end-users, but rather was available as “Optional Updates” for the user:

Now with WUfB-DS Policies we can centrally manage, which of these updates should be installed and which not. The end-user experience in this scenario is, all approved “Other” drivers will appear for the user like an “Recommended” Update and get installed automatically. This is especially useful for us for updates like Lenovo Firmware (UEFI) updates, which as far as we saw were always only a “Other” update, so the user had to manually select the update. It was also very helpful for us for drivers that get often updates like Intel network cards, where the “Recommended” updates are pretty old compared to the “Other” updates, which fixed a few issues for us.

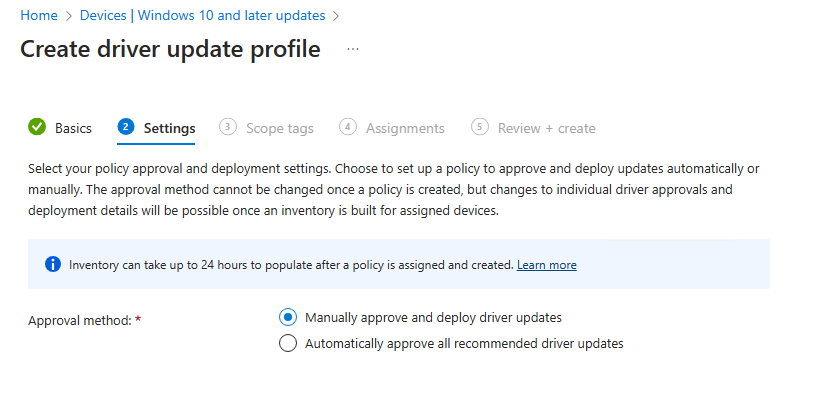
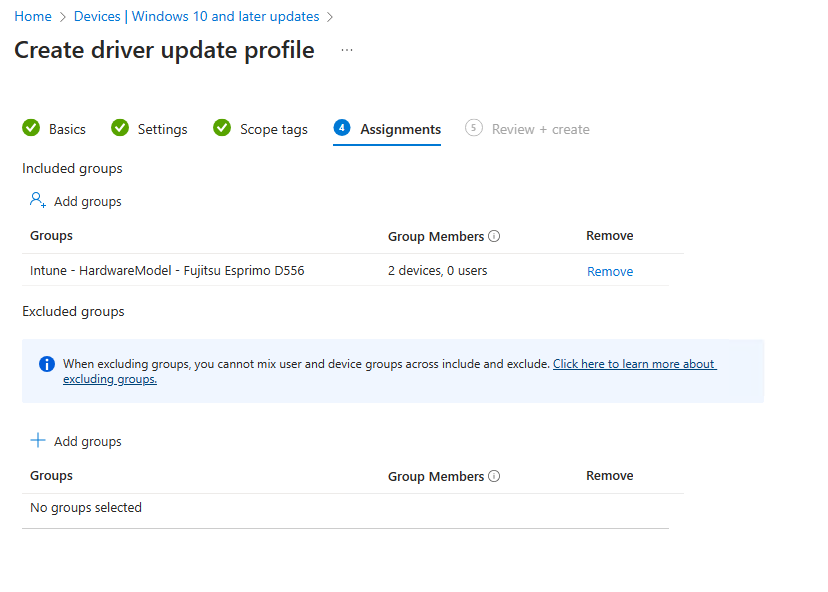
Manual Update Policies
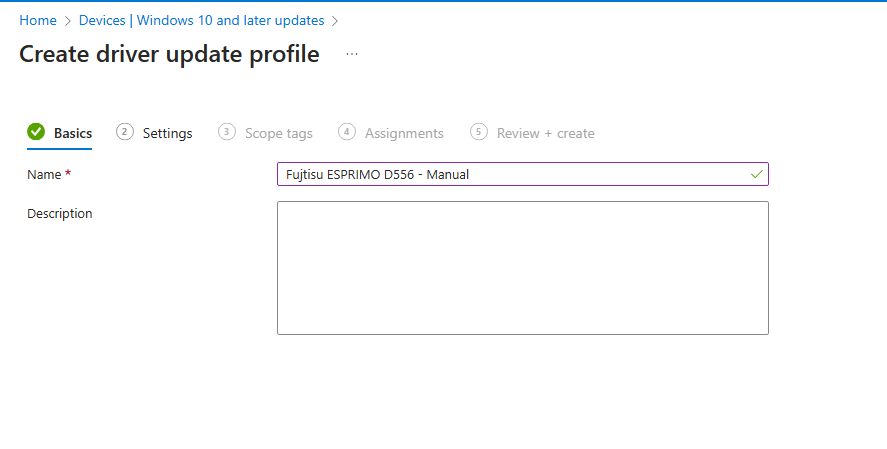
If the automatic approach that I’m using here sounds to dangerous for you, or you never had driver updates allowed via WUfB before, check out manual update policies. This way, you can get all the advantages like the possibility to “push” specific updates to the clients, but without the risk of getting a driver installed that you have not yet tested before.
The set-up process is pretty much the same as with the “Automatic” Policy, we will create a new policy, select manual and assign it to a group of devices that you want to manage:
Again, once the policy is created and synced with WUfB-DS you will be able to control updates. One helpful option for manual updates, is the “Drivers to review” in the update overview, while this count will always show “0” for automatic policy, it will show you a count of drivers in a manual policies that you can approve or block.

Reporting
With the integration of driver and firmware management in Intune, there are now also a few really cool reports available. A nice overview can be found in Windows Update Reports Overview:
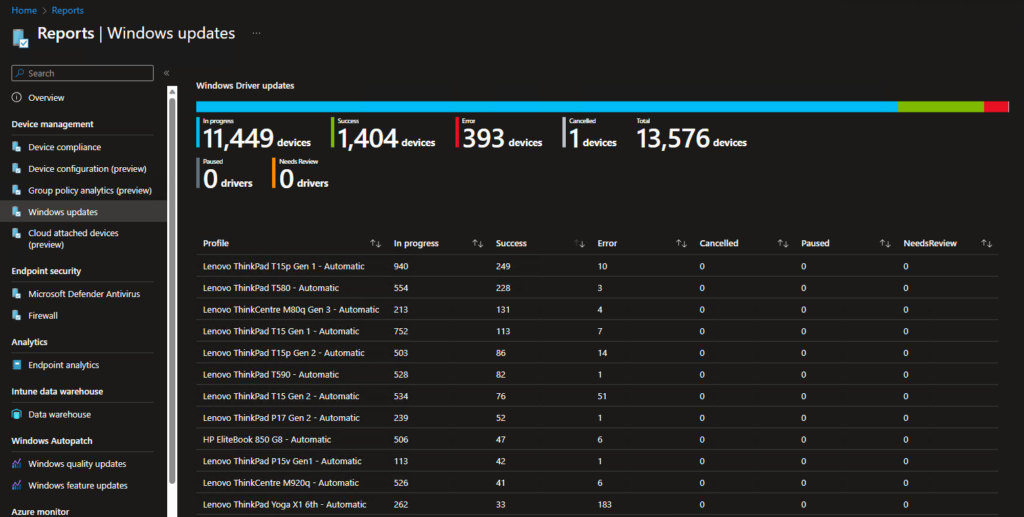
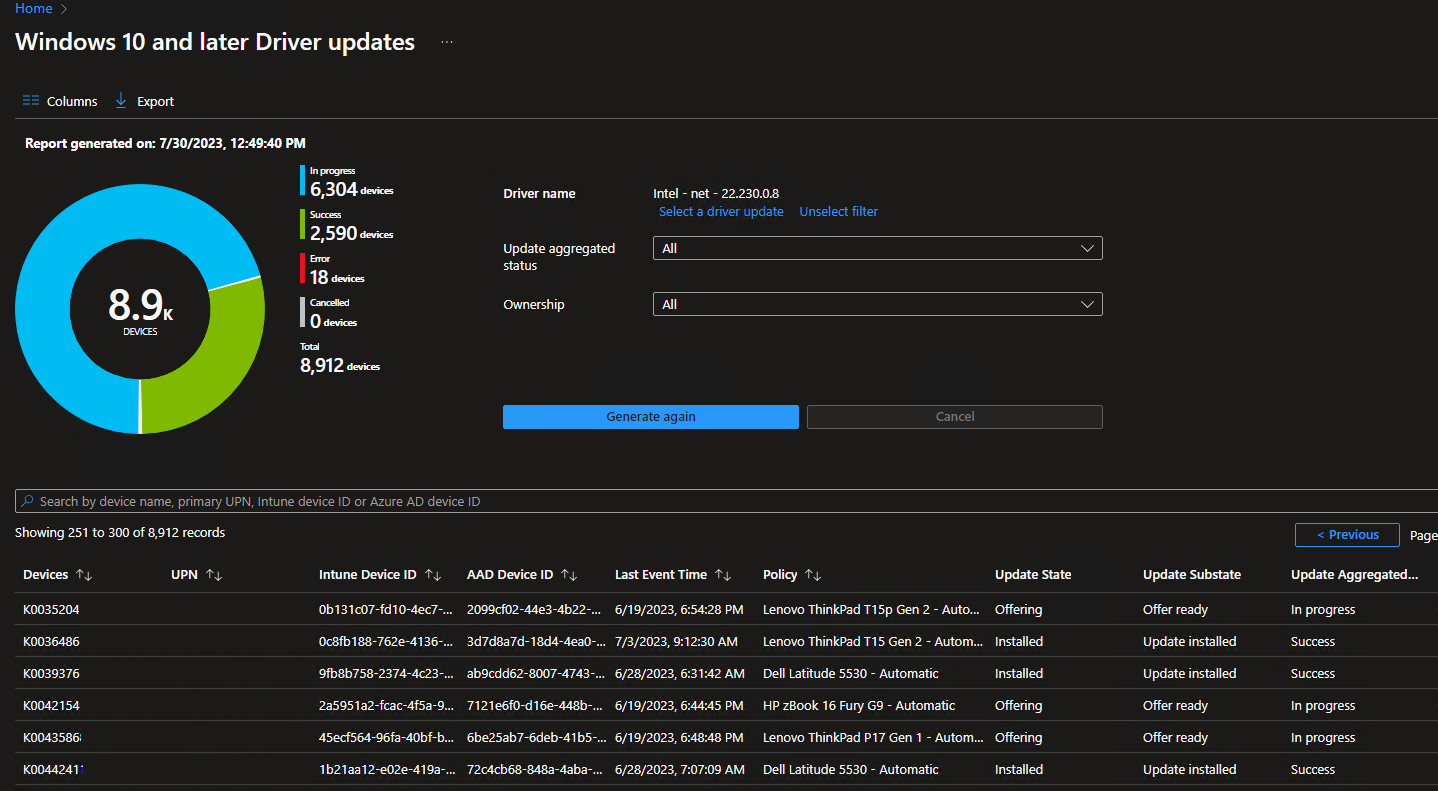
In the Reports blade there is also a more detailed per driver/firmware report available, where you can check the rollout status of each individual update.

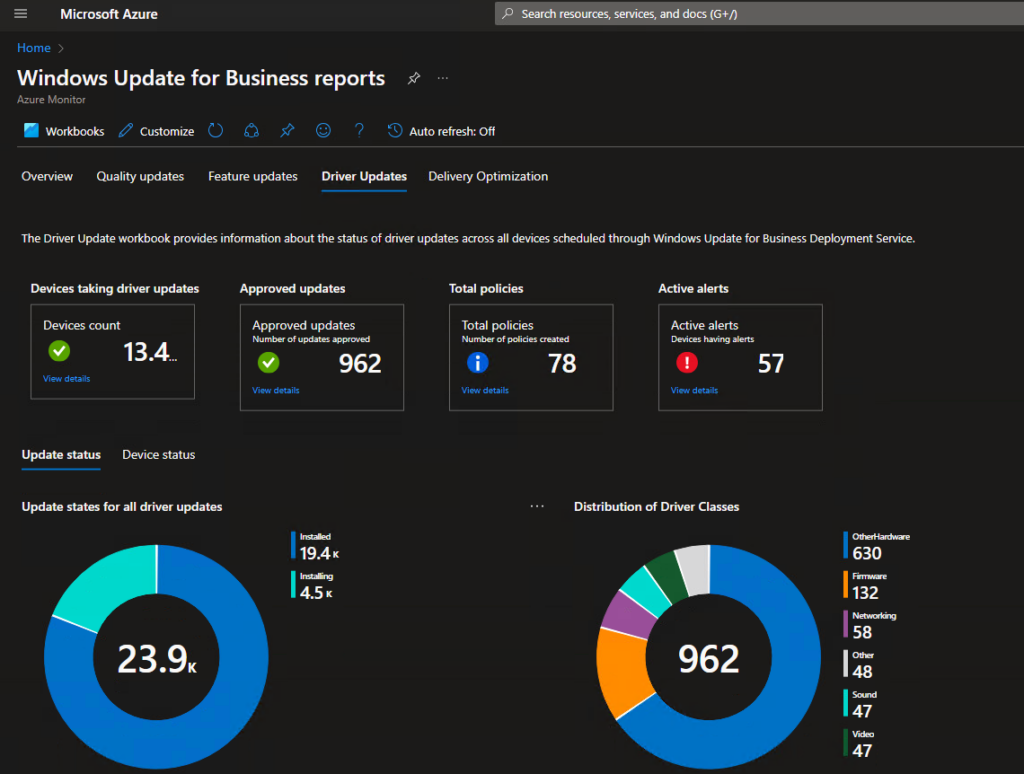
There is also a nice report available in the WUfB Reports (http://aka.ms/wufbreportsGA)
Leave a Reply